WireUnwired Brief:
WireUnwired Brief:
The Linux Foundation collaborates with Google and IBM to develop a Post-Quantum Cryptography Alliance
- Quantum Cryptography and Principles of Quantum Physics it is based on.
- Threats to traditional alogrithms explained with examples of Shor’s and Grover’s algorithm
- Some Quantum Attack Resistant algorithms Launched By NIST like CRYSTALS-KYBER, FALCON,SPHINCS+ etc.
- Two major Projects like OQS and PQ Code Package announced by Quantum crypto alliance.
A new initiative by the Linux Foundation, the Post-Quantum Cryptography Alliance (PQCA), has been launched with the support of major players in the tech industry, such as Google, IBM, and AWS. The goal of this alliance is to develop and standardize encryption algorithms that can resist the potential threats of quantum computing, which could break many of the current cryptographic schemes.
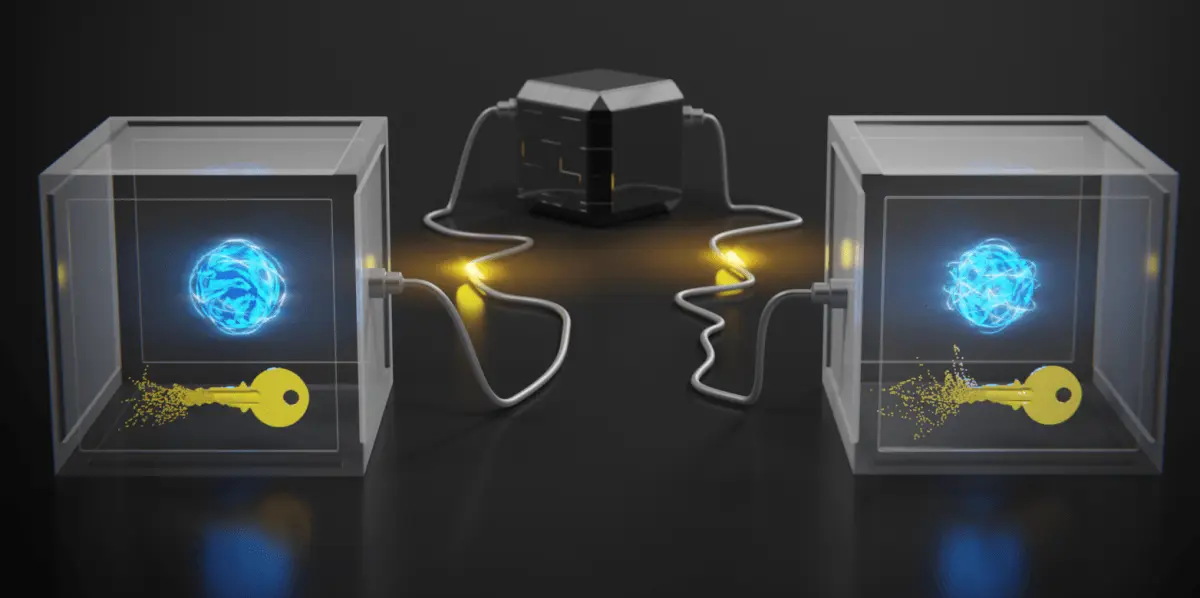
- Particles are inherently uncertain: On a quantum level, particles can simultaneously exist in more than one place or more than one state of being at the same time, and it is impossible to predict their exact quantum state.
- Photons can be measured randomly in binary positions: Photons, the smallest particles of light, can be set to have specific polarities, or spins, which can serve as a binary counterpart for the ones and zeros of classical computational systems.
- A quantum system cannot be measured without being altered: According to the laws of quantum physics, the basic act of measuring or even observing a quantum system will always have a measurable effect on that system.
- Particles can be partially, but not totally cloned: While the properties of some particles can be cloned, a 100% clone is believed to be impossible.
Threats to Traditional Algorithms from Quantum Computers
The Linux Foundation and its partners are working on developing encryption solutions that can resist the power of quantum computers. Quantum computers are machines that use the principles of quantum physics to perform calculations that are much faster and more complex than conventional computers. Quantum computers could potentially break the encryption methods that are currently used, exposing the data and communications of millions of users.
One of the methods that quantum computers could use to break encryption is Shor’s algorithm. This is a quantum algorithm for finding the prime factors of an integer, which is the basis of many encryption schemes, such as RSA. Shor’s algorithm can factor integers in polynomial time, meaning the time taken is proportional to the size of the integer, whereas classical algorithms take exponential time, meaning the time taken grows exponentially with the size of the integer. Shor’s algorithm works by converting the factoring problem to a period finding problem, which can be solved efficiently using quantum Fourier transform.
Quantum Attack Resistant Algorithms
To prevent these Security threats , the Quantum Encryption Alliance aims to create quantum-resistant encryption algorithms. These algorithms are based on mathematical problems that are hard to solve even for quantum computers. The alliance has chosen four algorithms from the NIST’s quantum encryption standardization projects as the starting point for its work. These algorithms are CRYSTALS-Kyber, CRYSTALS-Dilithium, Falcon, and SPHINCS+, which have been tested and verified to be secure against quantum attacks. The alliance will further improve and evaluate these algorithms to make them suitable for practical use.
The Quantum Encryption Alliance is a forward-looking response to the challenge of quantum computing, which could pose a serious threat to the security of current encryption technologies. By creating quantum-resistant encryption solutions, the alliance hopes to safeguard the privacy and integrity of data and communications in the quantum age.
Post-Quantum Cryptography alliance’s Major Initiatives
The Quantum Crypto Alliance has announced two major initiatives to promote openness and collaboration in the field of quantum encryption: the Open Quantum Safe project and the PQ Encryption Algorithm Project (PQ Code Package). The former is a groundbreaking open-source encryption algorithm that can withstand quantum computer attacks, while the latter aims to create a set of encryption levels based on the ML-KEM algorithm.
Additionally, the Quantum Crypto Alliance has made its existing resources available on GitHub for wider participation and engagement. Stakeholders and partners who are interested in quantum encryption can access these resources and contribute to the improvement and innovation of quantum encryption algorithms.
To sum up, the formation of the Post-Quantum Cryptography Alliance is an important step forward in the search for quantum-resistant encryption solutions. By leveraging the combined knowledge and resources of industry leaders, the alliance is ready to develop encryption technology that will protect sensitive information in the quantum computing era.
 WireUnwired Extra
WireUnwired Extra
Encryption is a process of transforming data into a form that is unreadable by anyone who does not have the key to decrypt it. The key is a secret piece of information that is used to encode and decode the data. Encryption is used to protect the confidentiality and authenticity of data and communications, especially in the digital world.
These are Articles
Microsoft pulls 70+ GitHub repos after malware breach
On Friday, 5th June 2026, GitHub disabled 73 Microsoft repositories in about 105 seconds after its alarms tripped. The trigger was a …
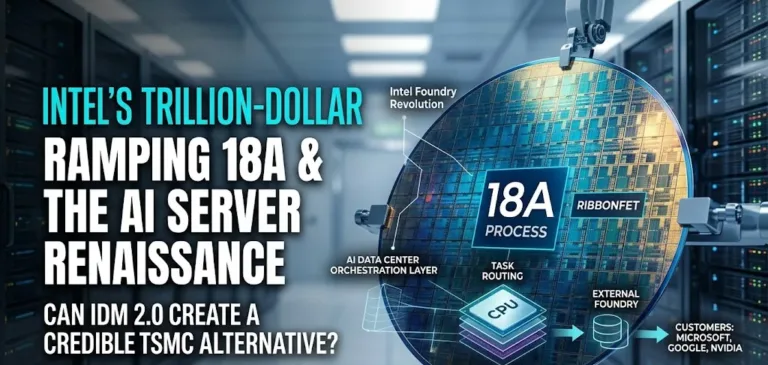
Intel's stock has surged 6x to over $120, but can its IDM 2.0 strategy and 18A process node justify the valuation? Dive into the trillion-dollar turnaround.
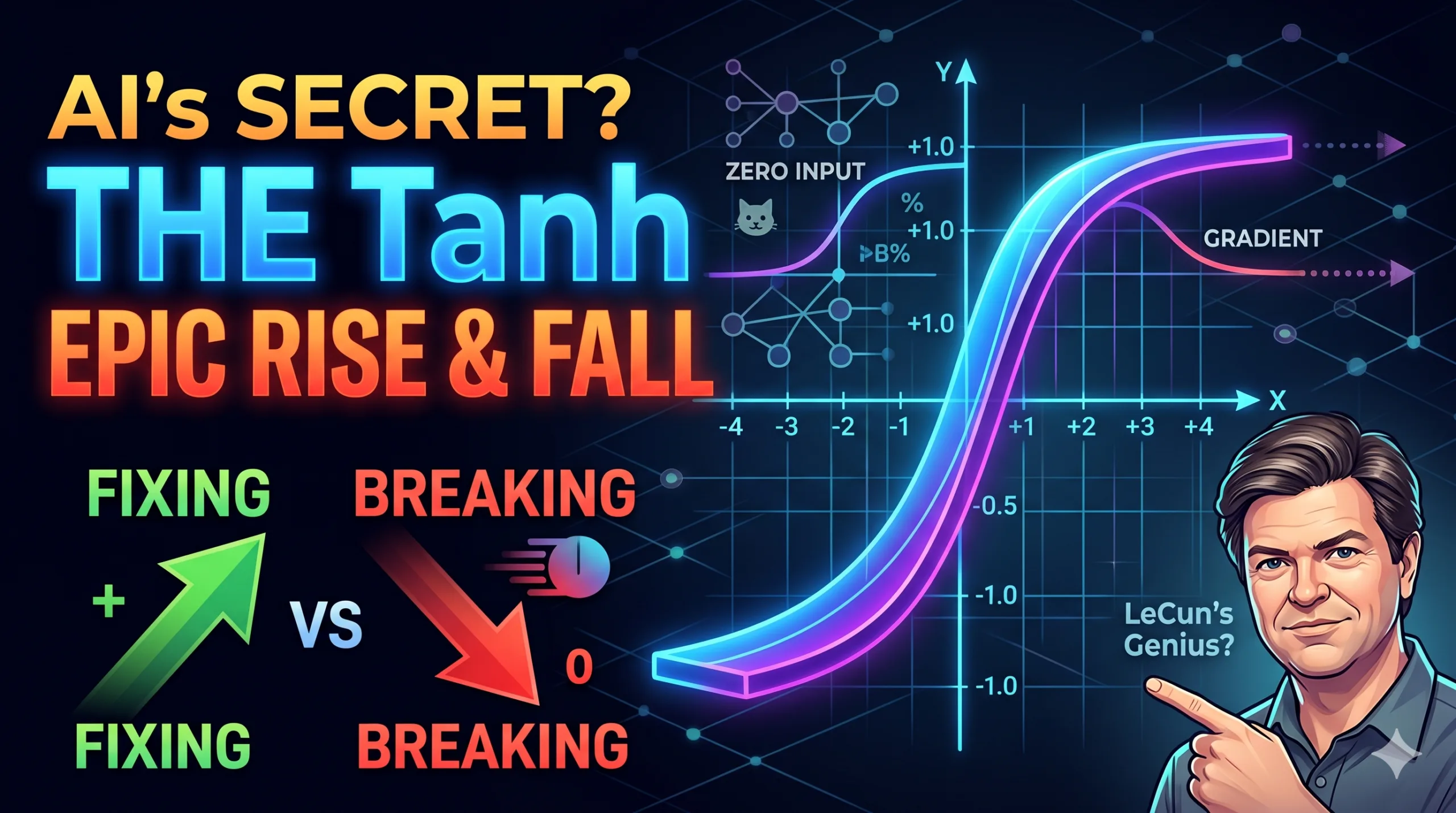
Tanh activation function came into existence to solve the weights sign problem but ended up with vanishing gradient problem,
Musk Faces Legal Defeat in case against OpenAI
Elon Musk has faced a legal defeat in his lawsuit against OpenAI and its leadership regarding the company’s transition from a nonprofit to a for-profit model.
Discover more from WireUnwired Research
Subscribe to get the latest posts sent to your email.

 WireUnwired Extra
WireUnwired Extra